Why VPN is Not Hiding Your Real Location (How to Solve It)
One of the VPN features is the ability to virtually change your location. It does that by masking your real IP address and using a VPN server to connect to websites on your behalf.
Changing the location allows you to access otherwise restricted content and browse privately. But does it hide your location all the time?
You probably noticed that websites sometimes still know your location even when on a VPN. So why is VPN not hiding your real location when it is supposed to?
Let’s see why you can still be discovered and how to solve it.
Why is VPN not hiding your location?
A VPN may not hide your location for a few reasons. First, the VPN you use might have IP leaks that reveal your real location. Second, websites use cookies, browser fingerprinting, and browser’s geolocation API to track you. A VPN can not hide your location completely if these methods are used.
Let’s take a look at possible reasons why VPN is not hiding your location.
Your VPN leaks IP address
There are three types of leaks: IP, DNS, and WebRTC leaks. IP leak protection is critical for a VPN to hide your location at all times. Even temporarily exposing your IP may reveal where you are, and it’s a serious privacy issue.
- IPv4 and IPv6 leaks: nowadays your ISP assigns you two types of IP – versions 4 and 6. VPN services mostly use IPv4 and block IPv6 addresses. If any of those are leaked your location is exposed to the websites.
- DNS leak: before connecting to a website your device makes a DNS query to turn a domain name into a website’s IP address. These queries are often leaked if a VPN is not configured properly. DNS leaks can reveal your real location and show the visited websites to your ISP.
- WebRTC leak: this type of leak is a browser-specific leak. A VPN apps have no control over it and it needs to be turned off in the browser settings. Find suggestions on how to turn it off below.
Websites use tracking cookies
Many websites use cookies either for functionality or tracking. Cookies can hold up information about your identity, location, and previously visited websites.
Unfortunately, a VPN can not block cookies as they are files that are downloaded inside a VPN tunnel. So even with your IP changed they still may reveal the information about where you are.
Some websites inject third-party cookies that can track you across the internet. These are mostly used by advertisers that can determine your approximate location.
Another tracking technique is called browser fingerprinting. It uses your browser’s parameters to partially identify you and your approximate location.
Your browser geolocation is used
Your location may be revealed by your browser GPS functionality. Some websites ask permission to use your browser’s geolocation API to let them know where you are. A VPN can not protect from that as all the coordinates are sent over the VPN, inside the encrypted tunnel. You should set browser location permissions manually as a VPN has no control over it.
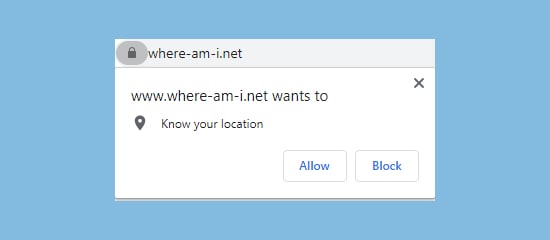
Most of the time websites detect your location by IP address. But, if browser geolocation is used your location is revealed even if you are connected to a VPN server.
You can test how this works at https://www.where-am-i.net/
Test Your VPN Knowledge – Take A Quiz!
How to hide your location using a VPN
There are still options for what you can do to fully hide your location when on a VPN. You need to tackle IP leaks, tracking, and deal with geo-location with simple steps.
Here’s how to hide your location on a VPN:
Test for IP leaks
To make sure your VPN truly works as intended you need to test for IP leaks. The easiest way to do so is to visit IP leak testing websites: www.ipleak.net or https://browserleaks.com/ip
Those will tell you if your real IPv4, IPv6, and DNS addresses are shown. It will display the results for WebRTC leak as well. In case a WebRTC leak is detected you need to install a VPN browser extension and disable the setting there. The best VPNs include those extensions in your subscription.
If any of those tests fail this means your VPN leaks your real location. You should seriously consider changing your service provider immediately. NordVPN or ExpressVPN are the leaders in the industry that do not leak any IPs.
Cut Off Tracking Cookies
A VPN on its own does not protect from tracking cookies. But, some services have features that can block malicious websites and advertiser tracking. They do protect from third-party cookies.
Another great tip is to use an incognito window. It is a privacy window that deletes all cookies after you close it. It starts your browsing session fresh each time and you can find it on every browser:
You can open Private Incognito Window in any browser by keyboard commands:
- Chrome: CTRL/Command + Shift + N
- Firefox: CTRL/Command + Shift + P
- Safari: Command + Shift + N
Disable geolocation on your browser
To hide your location on a VPN, you must configure your browser location permissions. Geolocation is the most common way to expose your coordinates even when connected to a VPN. You can do this on every browser.
Disable browser geolocation API On Chrome:
- Go to Menu > Settings
- Select Privacy and Security > Site Settings
- Then Location
- Turn on “Ask Before Accessing”
Disable browser geolocation API On Safari:
- Go to Preferences > Privacy
- Select Website Tracking
- Checkmark “Prevent cross-site tracking” and “Ask websites not to track me”
Disable browser geolocation API On Firefox:
- Go to Menu > Options
- Select> Privacy And Security
- Then Permissions > Location
- Add checkmark on “Block new requests” or manage permissions
Conclusion
When using a VPN your location might not be hidden all the time. This might happen because your VPN might leak your real IP address. The use of a browser geolocation API and cookies might also be one of the reasons.
Most of the time it is enough to hide your location with a VPN and blocking browser GPS settings. Here are the best VPNs to do that:
VPN Expert, BEng in Network Engineering

